LOADING
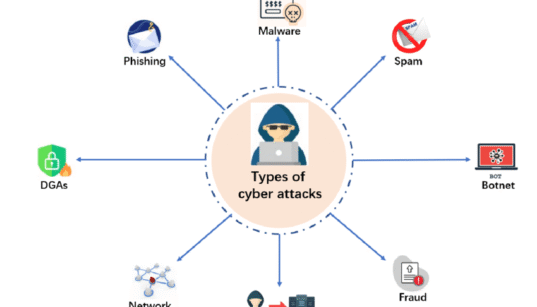
Cybersecurity
Welcome to our Cybersecurity category, where we delve into the latest trends and tools in online security. From in-depth reviews of security software to tips on best practices for data protection, this section aims to equip you with the knowledge to navigate the digital landscape securely. Stay informed about the digital threats facing your devices and discover effective solutions to ensure your personal and professional information remains safe.
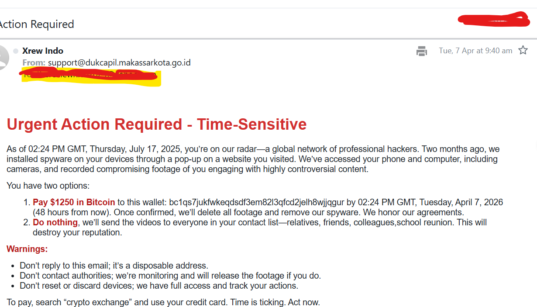
I Received a Threatening Email, Here’s Why It Was a Scam
April 14, 2026

How AI Is Powering Cyberattacks in 2026
April 5, 2026

Why Hackers No Longer Hack Systems, They Hack Identities
March 31, 2026

Identity-Based Cyberattacks: The Biggest Threat in 2026
March 28, 2026

Why Multi-Factor Authentication (MFA) Is Important
March 26, 2026

How to Secure Your Home Wi-Fi Network from Cyber Threats
March 4, 2026
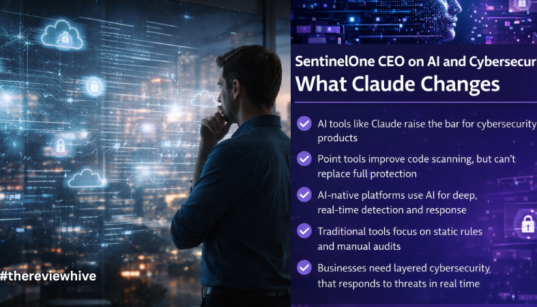
SentinelOne CEO on AI, Claude, and the Future of Security
February 26, 2026

How to Choose a Cybersecurity Service Provider for Small Business
February 25, 2026

Cyber Insurance Benchmarks for Small Businesses in 2026
February 19, 2026

Geopolitics Is a Defining Force in Cybersecurity
February 3, 2026

Supply Chain Cybersecurity Is Now a Business Survival Issue
January 28, 2026

Three Trends Redefining Cyber Risk in 2026
January 27, 2026

WhatsApp Links Used in Sophisticated Gmail Phishing Attack
January 20, 2026
Computer Parts That You Need to Clean Regularly
January 19, 2026

The Biggest Cyber Attacks of 2025
December 29, 2025
Why Traditional API Security Fails Against Generative AI-Driven Attacks
December 22, 2025
Generative AI Safety in Pentesting
November 26, 2025
Advantages of Generative AI for Pentesting
November 25, 2025

Top Zero Day Vulnerabilities 2025: Platform-Wise Breakdown
November 19, 2025
How Hackers Use WhatsApp Web
November 13, 2025

WhatsApp Two-Step Verification: Complete Setup and Best Practices
November 10, 2025

Role of Generative AI in Improving Cybersecurity
October 23, 2025

How Multi-Factor Authentication Protects Your Everyday Life
October 20, 2025

WhatsApp Worm Banking Malware: How It Spreads and How to Stay Safe
October 15, 2025

How Biometric Authentication is Redefining Digital Security in 2025
October 14, 2025

10 Facts Everyone Should Know About Cybersecurity in 2025
October 8, 2025

DarkGPT Pros and Cons: Power, Risks, and Real-World Impact
October 1, 2025

DarkGPT vs ChatGPT: Which Should You Trust—and Why
September 30, 2025

AI in Cybersecurity: How AI-Driven Threats and Defenses Are Shaping 2025
September 25, 2025

North Korean Hackers ChatGPT Phishing: Deepfake ID Used in Cyber Espionage
September 19, 2025

Do You Need to Upgrade to Windows 11 for Cybersecurity?
September 16, 2025

2025 Verizon DBIR: What Small- and Medium-Sized Businesses Need to Know
September 13, 2025

New Android Banking Trojan “RatOn” Can Drain Your Bank Accounts
September 12, 2025

Cyber-Attacks Expose Patient Data in Three French Regional Healthcare
September 11, 2025

Top 10 Benefits of Threat Intelligence
September 6, 2025

AI Cyberattacks: The Next Big Threat Businesses Can’t Ignore in 2025
September 4, 2025

Dutch Intelligence Confirms Cyberattacks by Chinese Group Salt Typhoon
September 4, 2025

How Claude AI Misuse Fuels Cybercrime
September 2, 2025

Shadow AI and Cyber Risks: The Hidden Threat Inside Enterprises
August 26, 2025

Cost of a Data Breach Report 2025: What Businesses Need to Know
August 25, 2025

Threat Intelligence Trends in 2025 – Use Cases, and What’s Next
August 13, 2025

How Threat Intelligence Works – The Full Lifecycle
August 8, 2025

What Is Cyber Threat Intelligence
August 7, 2025

5 Leading Cyber Security Predictions for 2025
August 5, 2025

Cold Wallets- A Preview
August 4, 2025

Top 10 Mac Antivirus for 2025
August 1, 2025

Top 10 cybersecurity courses in Virginia
July 28, 2025

CoinDCX Announces Global Recovery Bounty After $44M Hack
July 22, 2025

Why Telegram for Cybercriminals Still Works in 2025
July 9, 2025

How to Check if Your Password is Compromised
June 23, 2025