Tag: #VulnerabilityManagement
Generative AI is emerging as a transformative tool in identifying cyber vulnerabilities, offering innovative solutions that enhance cybersecurity efforts. With the rising sophistication of cyber threats, leveraging AI technologies has become essential for organizations to protect their digital assets effectively. This article delves into how Generative AI enhances vulnerability detection, simulates innovative attack vectors, and […]

Microsoft’s July security update reveals significant vulnerabilities, with attackers already exploiting flaws in the system. The update addresses a staggering 139 CVEs in Microsoft products and four in non-Microsoft products. The July update necessitates prompt action from administrators, given the patching requirements for 139 unique CVEs. Among these, two are actively exploited by attackers, and […]
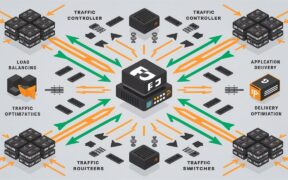
F5 BIG-IP malware has emerged as a serious threat to network security, exploiting vulnerabilities in widely used network traffic management devices. A recent report by Sygnia, a cybersecurity firm, details a concerning campaign by the suspected Chinese hacking group “Velvet Ant” that leveraged F5 BIG-IP malware to gain persistent network access and steal sensitive data […]
