80% of Ransomware Now Uses AI, Here’s What That Means
Share

AI-powered ransomware now plays a role in close to 80% of ransomware campaigns, based on recent cybersecurity research and industry reporting. At the same time, phishing continues to account for over 80% of initial access in cyberattacks, and more than 70% of ransomware incidents now include data exfiltration along with encryption. These are not isolated trends. Together, they show how ransomware has evolved into a fast, automated, and scalable threat.
Findings reported by Acronis and other sources highlight how ransomware groups are actively integrating artificial intelligence into their operations. In many cases, these capabilities are built into ransomware-as-a-service platforms, making advanced attacks accessible to a wider range of threat actors.
TL;DR
AI-powered ransomware is now used in nearly 80% of attacks. Attacks are faster and often unfold within hours. Phishing remains the main entry point and is now highly personalized using AI. Ransomware includes data theft and layered extortion. Traditional defenses are struggling. Businesses need stronger identity security, behavior-based monitoring, and continuous defense strategies.
The Rise of AI-Powered Ransomware
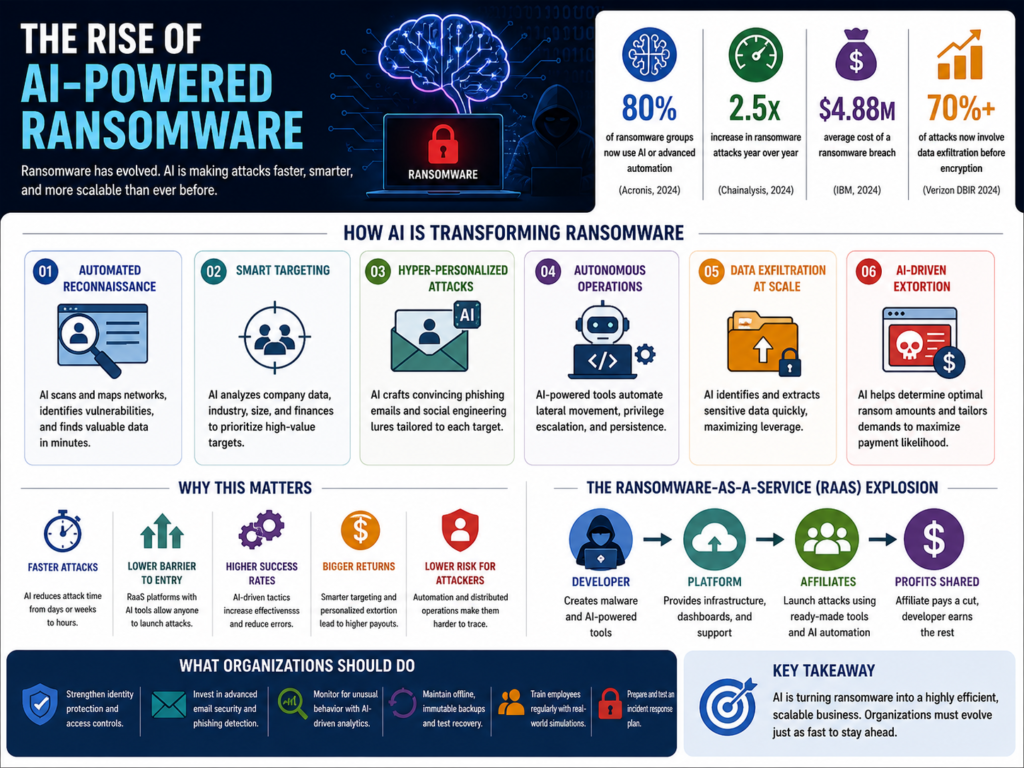
The rise of AI-powered ransomware is not about sudden innovation. It is about steady, practical adoption. Over the past few years, ransomware groups have started using artificial intelligence to remove friction from their operations. Reports referenced by Acronis and other industry analyses show that close to 80% of ransomware groups now integrate AI or advanced automation into their workflows. This reflects a clear shift from manual, skill-heavy attacks to systems that can run with minimal input.
- What makes this change important is accessibility. Attackers are not building complex AI models from scratch. They are using existing tools to automate key stages of the attack chain. Tasks like writing phishing emails, scanning networks, identifying vulnerabilities, and prioritizing targets can now be handled quickly and at scale.
- This shift is closely tied to the growth of ransomware-as-a-service. These platforms provide ready-made infrastructure, including dashboards, payment handling, and attack kits. AI features are now being added to these offerings, allowing even less experienced actors to run effective campaigns. As a result, the number of attackers has increased, not just their capability.
- Another factor is consistency. AI reduces human error. It helps standardize processes, which leads to more predictable outcomes. Attackers can test different approaches, analyze results, and refine their methods without slowing down operations. This makes ransomware campaigns more reliable and repeatable.
- There is also a broader trend across malware. Research indicates that a large share of modern malware now includes some level of automation or AI-driven functionality, reinforcing the idea that ransomware is part of a wider transformation in cyber threats.
The rise of AI-powered ransomware is not about replacing attackers. It is about enhancing them. It allows them to move faster, target more effectively, and scale their operations without increasing effort. That combination is what makes this shift significant.
The Shift to Machine-Speed Attacks
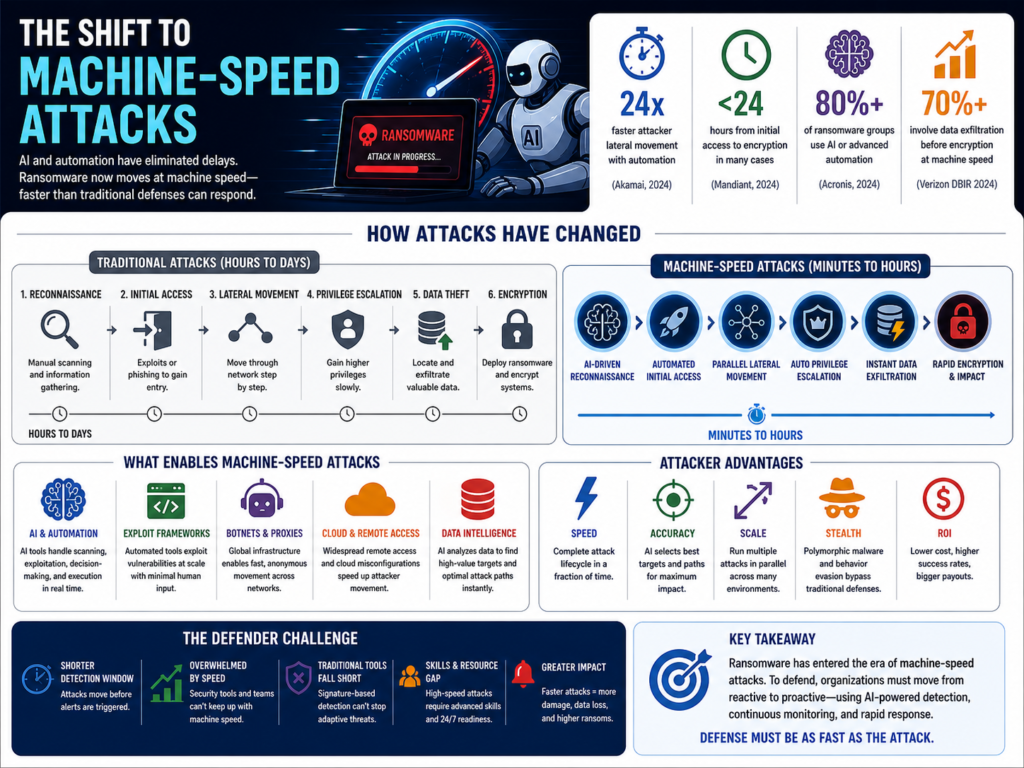
The biggest change in ransomware today is speed. AI has removed many of the delays that once slowed attackers down, turning what used to be a staged process into something that can unfold almost continuously.
- In earlier attacks, reconnaissance took time. Attackers had to probe systems manually, test vulnerabilities, and map networks step by step. Now, AI-driven tools can scan entire environments in minutes. They identify weak points, map relationships between systems, and flag high-value data without much human input.
- This shift has a direct impact on how quickly attacks progress. Security research shows that many ransomware incidents now move from initial access to lateral movement within hours. In more advanced cases, critical stages of the attack chain can be completed in under 24 hours. That leaves very little time for detection or response.
- Automation also changes what happens after entry. Once inside, attackers no longer need to guide every step. AI-assisted workflows can escalate privileges, move across systems, and prepare data for exfiltration. These actions can run in parallel, which further reduces the overall attack timeline.
- Polymorphic malware adds another layer to this speed. Instead of using static code, AI allows malware to modify itself as it operates. This helps it avoid detection while continuing to execute. Traditional tools struggle here because they rely on recognizing known patterns, and those patterns no longer stay consistent.
- There is also a decision-making element. Some ransomware operations now use AI to analyze a target’s environment and suggest the most effective path forward. This can include identifying critical systems, estimating financial capacity, and even shaping ransom demands based on available data.
The result is what many now describe as machine-speed attacks. The attack cycle is faster, more coordinated, and less dependent on human timing. For defenders, this creates a gap. Security teams are still structured around investigation and response, which takes time. AI-driven attacks are designed to move before those responses can fully take effect. This is not just an increase in speed. It is a change in how attacks are executed.
Hyper-Personalized Social Engineering
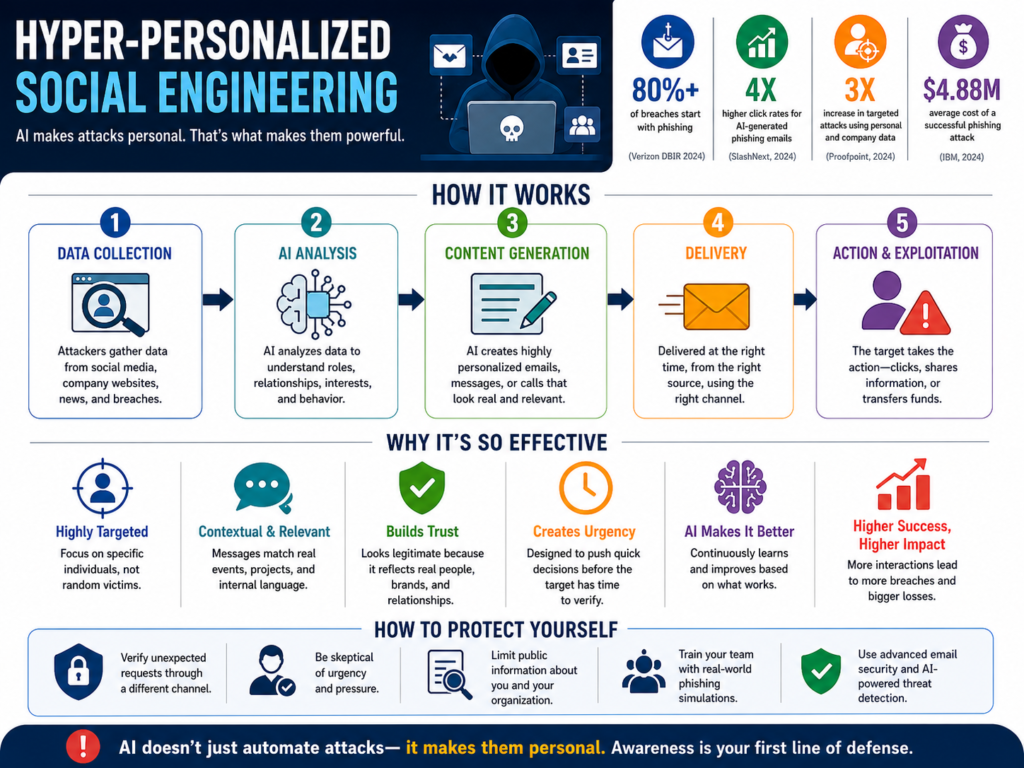 Social engineering has always been the easiest way in. What’s changed is how precise it has become. Phishing still drives the majority of initial access. Most industry reports place it at over 80% of breaches, and that hasn’t shifted. What has changed is the quality of the attack. AI has removed the usual signs people were trained to spot.
Social engineering has always been the easiest way in. What’s changed is how precise it has become. Phishing still drives the majority of initial access. Most industry reports place it at over 80% of breaches, and that hasn’t shifted. What has changed is the quality of the attack. AI has removed the usual signs people were trained to spot.
- Emails are no longer generic. Attackers use AI tools to study publicly available data, internal communication patterns, and role-specific language. The result is messages that read like they belong inside the organization. They reference real projects, use familiar tone, and often arrive at the right moment. This makes them harder to question.
- There’s also a shift from broad campaigns to targeted ones. Instead of sending thousands of emails and hoping for a few clicks, attackers focus on specific individuals. Finance teams, executives, and IT staff are common targets because of the access they hold. AI helps build these profiles quickly and at scale.
- Voice-based attacks have also improved. AI-generated voice cloning allows attackers to impersonate senior leaders with a high level of accuracy. These calls often create urgency, asking for immediate transfers or access changes. The combination of authority and timing makes them effective.
- Another layer is contextual phishing. AI-generated messages can align with real-world events. For example, emails tied to invoices, vendor changes, or internal updates. These are not random messages. They fit into ongoing workflows, which lowers suspicion.
- This creates a problem for traditional awareness training. Employees are often taught to look for poor grammar, unusual phrasing, or obvious inconsistencies. Those signals are no longer reliable. AI-generated content is clean, structured, and consistent.
- There is also less room for hesitation. Many of these attacks are designed around urgency. A request that looks legitimate and time-sensitive can push someone to act before verifying. The end result is simple. Social engineering is no longer about tricking large groups. It is about convincing specific people. AI makes that process faster, more accurate, and easier to scale.
For organizations, this means human risk has increased. Technical controls still matter, but user behavior is now a critical part of the defense. Training needs to move beyond basic awareness and focus on real-world scenarios that reflect how these attacks actually look today.
Ransomware Is No Longer Just About Encryption
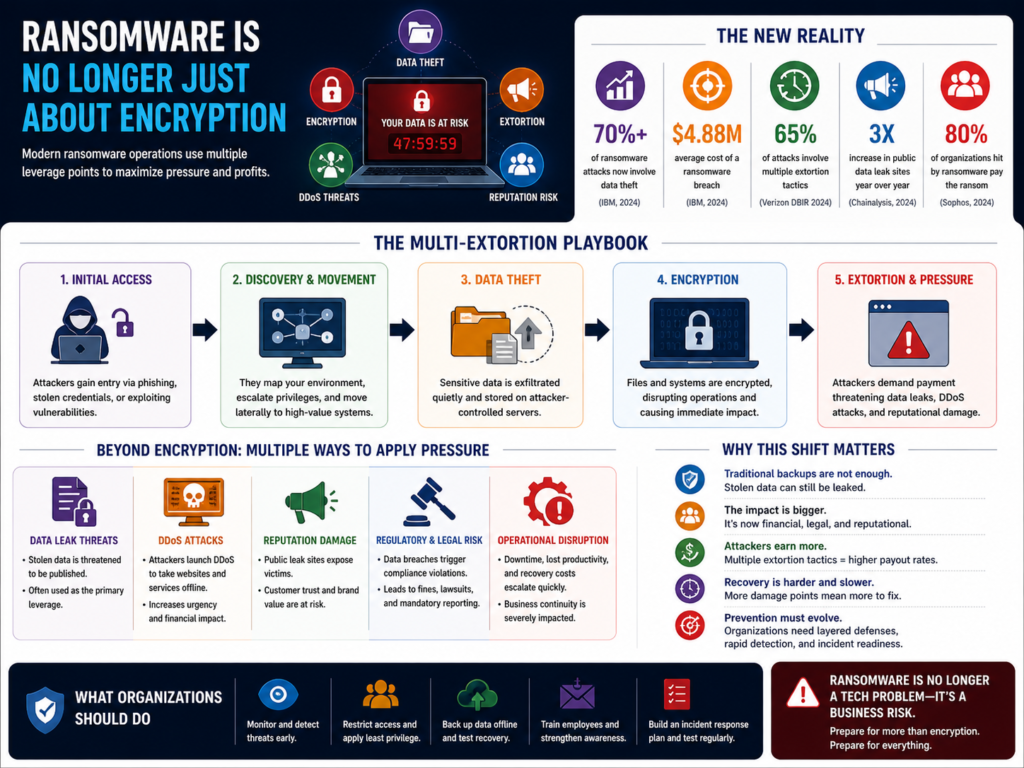 Ransomware used to follow a simple model. Attackers would break in, encrypt files, and demand payment to restore access. That model still exists, but it is no longer the full picture. Today, ransomware is built around leverage, not just disruption.
Ransomware used to follow a simple model. Attackers would break in, encrypt files, and demand payment to restore access. That model still exists, but it is no longer the full picture. Today, ransomware is built around leverage, not just disruption.
- One of the biggest shifts is the rise of data exfiltration. In most modern incidents, attackers steal sensitive data before encrypting systems. Industry reporting shows that over 70% of ransomware attacks now include data theft as part of the operation. This changes the pressure on victims. Even if backups are available, the risk of data exposure remains.
- This is where double and triple extortion come in. Attackers don’t just demand payment for decryption. They threaten to leak stolen data publicly or sell it on underground forums. In some cases, they add another layer by launching distributed denial-of-service attacks to increase urgency. The goal is to make non-payment as painful as possible.
- AI is making this process faster and more targeted. Instead of stealing everything, attackers can identify high-value data quickly. Financial records, customer databases, legal documents, and internal communications are prioritized. This reduces noise and increases the impact of the threat.
- Another major change is how attackers gain and maintain access. There is a clear shift toward credential-based attacks. Instead of forcing entry through vulnerabilities, attackers use stolen usernames and passwords to log in. Security research continues to show that a growing share of breaches now involve valid credentials rather than exploits.
- AI supports this shift by speeding up credential harvesting and password attacks. It can automate login attempts, analyze patterns, and bypass basic protections. Once inside, the activity often blends in with normal user behavior, making detection more difficult.
- This also changes how ransomware spreads within a network. Instead of noisy, aggressive movement, attackers move quietly. They map systems, identify key assets, and escalate privileges before triggering the final stage of the attack.
- The financial model has evolved as well. Ransom demands are no longer random. In some cases, attackers analyze a target’s size, revenue, and even cyber insurance coverage to determine how much to demand. This makes negotiations more calculated and increases the likelihood of payment.
What this means in practice is simple. Encryption is now just one part of a broader strategy. The real power of modern ransomware comes from combining access, data theft, and pressure into a single operation. For organizations, this raises the stakes. Recovery is no longer just about restoring files. It’s about managing data exposure, legal risk, and reputational damage at the same time.
Why Traditional Security Is Struggling
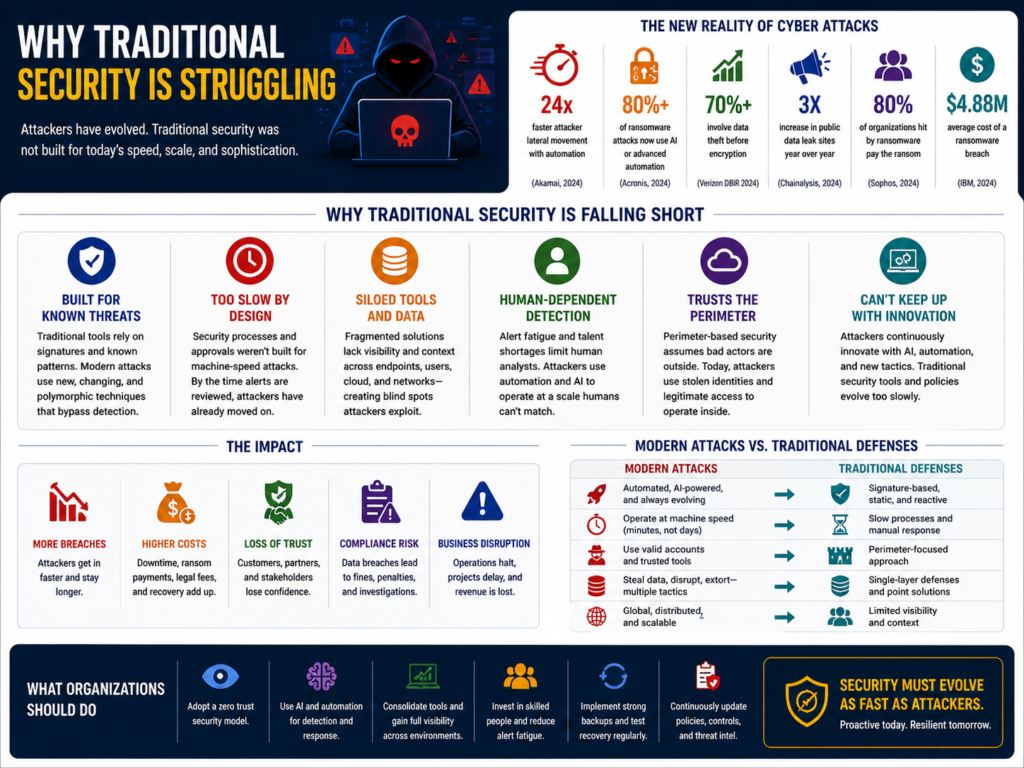
Traditional security isn’t failing because it’s useless. It’s failing because it was built for a different kind of threat. Most legacy defenses were designed to stop known malware, predictable attack patterns, and slower, human-driven campaigns. AI-powered ransomware doesn’t follow those rules.
- The first problem is how detection works. Many organizations still rely on signature-based tools. These systems look for known malware patterns. But modern ransomware doesn’t stay the same long enough to be recognized. AI helps generate polymorphic code that keeps changing. By the time a signature is created, the malware has already evolved.
- The second issue is speed. Traditional security assumes there’s time to detect and respond. That assumption no longer holds. AI-driven attacks move quickly, often progressing from initial access to lateral movement within hours. In some cases, full compromise happens in under a day. Security teams are left reacting to alerts after the attacker has already established control.
- There’s also a visibility gap. Many tools are focused on perimeter defense, keeping attackers out. But attackers are no longer forcing entry in the same way. A growing number of breaches now involve valid credentials. This means attackers log in through legitimate channels. Once inside, their activity can look normal, which makes detection harder.
- Another limitation is tool fragmentation. Organizations often rely on multiple disconnected security solutions. Each tool sees only a part of the activity. Without a unified view, early warning signs are missed. AI-powered attacks take advantage of this by moving quietly across systems.
- Alert fatigue adds to the problem. Security teams deal with a high volume of alerts every day. Many of these are false positives. When real threats appear, they can get lost in the noise. AI-driven attacks are designed to blend in, which makes them even harder to prioritize.
- Finally, traditional security is mostly reactive. It responds after something suspicious is detected. But AI-powered ransomware is proactive. It scans, adapts, and executes without waiting. This creates a mismatch. Defenders are responding to events that have already moved forward.
The challenge is not just better tools. It’s a shift in approach. Security needs to focus on behavior, identity, and continuous monitoring rather than relying only on known threat signatures.
What Businesses Need to Do Now

Organizations need to adapt their approach to security.
- Behavior-based detection is becoming essential. Monitoring activity and identifying anomalies can help detect threats early. Endpoint Detection and Response solutions support this approach.
- Identity security must be strengthened. Strong, phishing-resistant multifactor authentication reduces the risk of unauthorized access.
- The Zero Trust model is also important. It requires continuous verification of users and devices, limiting lateral movement within networks.
Basic practices remain relevant. Regular patching reduces vulnerabilities. Secure and tested backups ensure recovery is possible without paying a ransom. These measures must work together as part of a broader, proactive strategy.
Real-World Impact Of AI-powered Ransomware
The impact of AI-powered ransomware is already measurable, and the numbers show how quickly the threat is scaling.
- Recent industry reporting tied to findings from Acronis and other cybersecurity analyses confirms that nearly 80% of ransomware groups now integrate AI or automation into their operations. This has directly reduced the time between initial access and full compromise. In many modern incidents, attackers move laterally within hours, not days, with some advanced campaigns completing critical stages of the attack chain in under 24 hours.
- Phishing continues to be the primary entry point. Studies across security platforms consistently show that over 80% of cyberattacks begin with phishing or social engineering, and AI has significantly increased its effectiveness. AI-generated phishing emails are more convincing, better written, and context-aware, which has led to higher engagement rates and fewer early detections.
- The nature of ransomware itself has also changed. It is no longer limited to encrypting files. Current data suggests that more than 70% of ransomware attacks now include data exfiltration, meaning attackers steal sensitive information before locking systems. This shift has made extortion more effective, as organizations face the risk of public data exposure in addition to operational disruption.
- Financial impact remains severe. Global estimates indicate that the average cost of a ransomware attack often exceeds $1 million when factoring in downtime, recovery, legal costs, and reputational damage. For small and mid-sized businesses, these costs can be difficult to absorb, which is why attackers increasingly target organizations with weaker defenses.
- Another notable trend is the shift toward identity-based attacks. Security research shows that a growing share of breaches now involve valid credentials rather than traditional exploitation techniques. Attackers are logging in instead of breaking in, using stolen usernames and passwords to bypass perimeter defenses. AI supports this by accelerating credential harvesting and password cracking efforts.
- There is also a broader pattern across malware as a whole. Reports indicate that up to 80% of modern malware now incorporates some level of AI or automation, reinforcing the idea that ransomware is part of a larger transformation in cyber threats.
Taken together, these figures point to a clear conclusion. AI has not just improved ransomware. It has changed how consistently and efficiently it can be executed. The result is a threat landscape where attacks are faster, more targeted, and more difficult to stop once they begin. The financial impact is significant. The overall cost of ransomware incidents, including recovery and downtime, often exceeds one million dollars globally.
Key Ransomware Trends to Watch (2026)
|
Trend |
What’s Happening |
Why It Matters |
What to Watch |
|
AI-powered ransomware |
Around 80% of ransomware campaigns now use AI or automation |
Attacks are faster, more scalable, and require less skill |
Growth of AI-driven attack kits in ransomware-as-a-service |
|
Machine-speed attacks |
Attacks move from entry to execution within hours, sometimes under 24 hours |
Reduces response time for defenders |
Shorter dwell time and faster lateral movement |
|
Hyper-personalized phishing |
AI-generated emails mimic tone, context, and internal communication |
Higher success rates and harder detection |
Targeted attacks on finance, HR, and leadership roles |
|
Rise of deepfake attacks |
Voice cloning used for vishing and fraud |
Increases trust-based exploitation |
Executive impersonation and urgent request scams |
|
Data exfiltration first |
Over 70% of attacks now involve data theft before encryption |
Increases pressure to pay ransom |
Growth of data leak sites and public exposure threats |
|
Triple extortion |
Encryption, data theft, and DDoS combined |
Amplifies damage and urgency |
Multi-layered ransom demands |
|
Credential-based attacks |
Attackers log in using stolen credentials instead of exploiting systems |
Bypasses traditional perimeter defenses |
Increase in identity-related breaches |
|
Decline of signature-based detection |
Polymorphic malware evades traditional antivirus |
Reduces effectiveness of legacy tools |
Shift toward behavior-based detection |
|
Targeting SMBs |
Smaller businesses are increasingly targeted |
Often weaker defenses and higher likelihood of payment |
More frequent attacks on mid-sized firms |
|
Ransomware as a business model |
RaaS platforms scale operations and standardize attacks |
Lowers entry barrier for attackers |
Expansion of affiliate-based cybercrime ecosystems |
|
AI-driven decision making |
AI helps attackers choose targets and ransom amounts |
More calculated and effective attacks |
Personalized ransom demands based on company data |
|
Increased automation across malware |
Up to 80% of malware now includes automation or AI elements |
Indicates broader shift beyond ransomware |
Convergence of AI across all cyber threats |
The Economics Behind AI-Driven Cybercrime
Ransomware has moved from isolated attacks to a structured business model. AI is what makes that model efficient.
- At a basic level, cybercrime now runs like an operation with inputs, processes, and returns. AI reduces the cost of each step. Tasks that once required time and expertise, such as writing phishing emails, scanning networks, or selecting targets, are now automated. This lowers the barrier to entry and allows more attackers to participate.
- The rise of ransomware-as-a-service has reinforced this model. These platforms provide ready-made infrastructure, including dashboards, payment systems, and support channels. AI features are now built into many of these offerings, which means attackers can run campaigns without deep technical knowledge. The focus shifts from skill to execution.
- This also changes how attackers scale. Instead of focusing on a few high-value targets, they can run multiple campaigns at once. AI helps test different approaches, track results, and refine tactics quickly. What works gets repeated. What fails is adjusted. This creates a feedback loop that improves success rates over time.
- Revenue strategies have become more calculated. Attackers no longer set random ransom amounts. In some cases, they analyze a target’s size, industry, and financial position to estimate what the organization can afford to pay. This increases the likelihood of payment and reduces negotiation time.
- Costs on the attacker side are relatively low compared to potential returns. Once tools and infrastructure are in place, each additional attack requires minimal effort. This makes ransomware highly scalable. A single group can run dozens of campaigns in parallel.
- There is also a shift in risk management. By using automation and distributed operations, attackers reduce their exposure. Responsibilities are often split across different roles, from developers to affiliates. This structure makes it harder to trace activity back to a single source.
- The broader trend supports this model. Reports suggest that a large share of modern malware now includes automation or AI-driven components. This means ransomware is part of a wider move toward efficiency in cybercrime.
What this leads to is a stable and repeatable system. AI does not just improve attacks. It makes them more predictable from the attacker’s perspective. That predictability is what allows ransomware to operate as an ongoing business rather than a one-off event.
Key Takeaways
- AI-powered ransomware is now used in most ransomware attacks
- Cyberattacks are happening faster, often within hours
- Phishing remains the primary entry point and is now highly personalized
- Over 70% of ransomware attacks involve data theft along with encryption
- Credential-based attacks are replacing traditional break-in methods
- Traditional antivirus tools are not sufficient on their own
- Identity security and multifactor authentication are critical
- Behavior-based detection improves early threat identification
- Zero Trust helps limit the spread of attacks within networks
- Ransomware has become a scalable and structured cybercrime model
To Sum Up
AI has changed how ransomware operates, not what it aims to do. The focus is still on disruption and financial gain, but the execution is faster, more precise, and easier to scale. This shift reduces the margin for error on the defender’s side. Organizations can no longer rely on delayed detection or isolated tools. Security needs to be continuous, layered, and aligned with how modern attacks actually work.
FAQs
What is AI-powered ransomware?
AI-powered ransomware is a type of cyberattack where artificial intelligence is used to automate tasks such as phishing, vulnerability scanning, and attack execution.
Why are ransomware attackers using AI?
Attackers use AI to improve speed, accuracy, and scalability. It allows them to run more campaigns with less effort and higher success rates.
How does AI improve phishing attacks?
AI enables attackers to create highly personalized emails and messages that mimic real communication, making them harder to detect.
Is ransomware more dangerous in 2026?
Yes. Ransomware is faster, more targeted, and more difficult to detect due to the use of AI and automation.
What is the best way to defend against AI-powered ransomware?
A strong defense includes behavior-based detection, multifactor authentication, Zero Trust architecture, regular patching, and secure backups.










