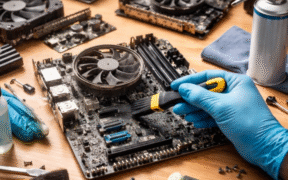
A computer is used every day in many homes and offices. It runs for long hours. It also sits in one place most of the time. Because of this, dust slowly builds up on its parts. Many users clean only the screen or keyboard. They forget about the inside parts. This habit leads to heat […]
A newly disclosed Bluetooth vulnerability has raised serious privacy concerns for users of wireless headphones, earbuds, and speakers. Security researchers have found that a flaw in the Google Fast Pair system can allow attackers to silently connect to nearby Bluetooth audio devices, track their location, and even listen through built-in microphones, all without the owner’s […]
A China-linked hacking group has expanded a long-running cyber-espionage campaign against telecom providers by exploiting known vulnerabilities in edge networking devices. This breach highlights growing risks to telecommunications security and the critical need for stronger defenses in global network infrastructure. The recent incidents involving China-linked Hackers Breach Telecom Networks underscore these threats. Security teams at […]